Pattern Language of Modern Power by Steafon Perry
Table of Contents
- What Is This Book About?
- Who Should Read It?
- The Standards of Evidence Rubric: Why It Matters
- Chapter-by-Chapter Highlights
- The Financial Architecture Appendix
- What the Book Gets Right
- What Has Been Strengthened in This Edition
- How It Compares to Similar Works
- Frequently Asked Questions
1. What Is This Book About?
The Hidden Hand: Then and Now by Steafon Perry is a structural investigation into how power operates in modern democratic societies. It is not a conspiracy theory. It is a documented analysis drawing exclusively from declassified government records, congressional testimony, peer-reviewed research, and investigative journalism.
The book traces what Perry calls the “pattern language of modern power”: eight recurring mechanisms through which influence is exercised, narratives are shaped, crises are leveraged, and dissent is managed. Those mechanisms are media management, language manipulation, crisis creation, opposition management, military expansion, elimination, surveillance, and financial architecture.
The starting point is a 1926 antisemitic text by Cherep-Spiridovich. Perry strips that text of its poisoned framing and examines its structural observations against the documented record. The patterns are real. The attribution is wrong. The distance between those two facts is where the book lives.
2. Who Should Read It?
This book is for:
- Readers of documented history who want to understand how power actually operates, not how it presents itself
- Students of political science, media studies, economics, and history
- Journalists, researchers, and policy analysts
- Anyone who has felt that official explanations leave something out and wants tools, not fear
- Readers of Noam Chomsky, C. Wright Mills, Carroll Quigley, and Shoshana Zuboff
It is not for readers seeking confirmation of any particular political tribe. The structural patterns documented here have been exploited by actors across the entire ideological spectrum.
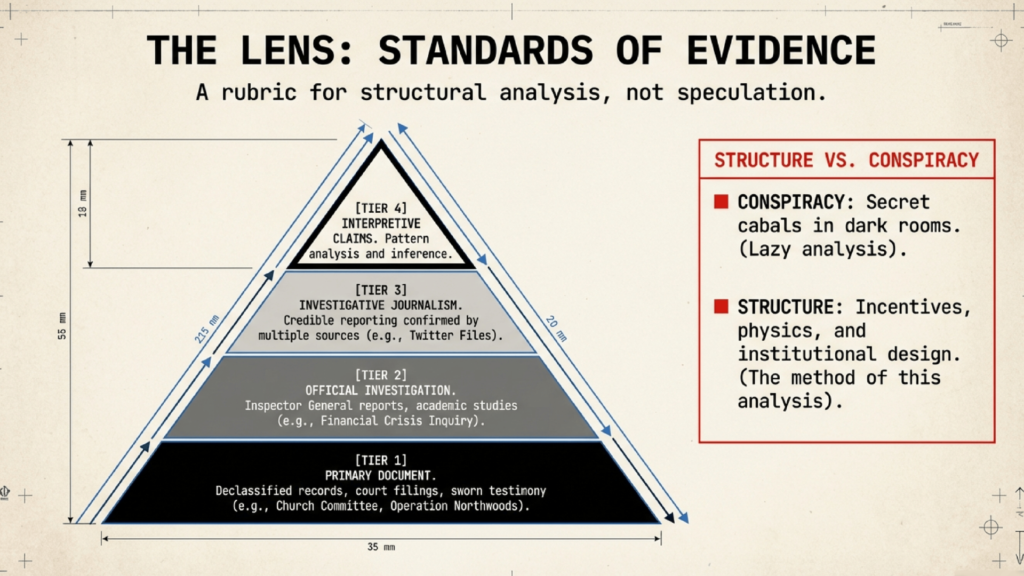
3. The Standards of Evidence Rubric: Why It Matters
One of the book’s most distinctive contributions is its one-page Standards of Evidence Rubric, applied consistently throughout the text. Every significant claim is labeled:
- [TIER 1] Primary Document: Declassified government records, congressional testimony, court filings
- [TIER 2] Official Investigation or Peer-Reviewed Research
- [TIER 3] Reputable Investigative Journalism confirmed by multiple sources
- [TIER 4] Contested or Interpretive Claims, clearly labeled as inference
The rubric is accompanied by Hard Constraints the book explicitly observes: no institution is described as omnipotent, no ethnic or religious group is assigned collective responsibility, correlation is not treated as causation, and the absence of confirming evidence is not treated as evidence of concealment.
This framework makes the book falsifiable in a way that most works in this genre are not. Readers can verify every Tier 1 claim directly through the National Security Archive, the CIA Electronic Reading Room, and the bibliography.
4. Chapter-by-Chapter Highlights
Chapter 1: The Anatomy of a Playbook
Traces the structural relationship between private finance and political power from the Rothschild banking network through the Jekyll Island meeting of 1910 and the creation of the Federal Reserve. Introduces the eight elements of the playbook.
Chapter 2: The Press Is the Weapon
Documents Operation Mockingbird, the propaganda model of Chomsky and Herman, the consolidation of U.S. media to six corporations controlling 90 percent of content, the Overton Window, the Twitter Files, and the algorithm as editor.
Chapter 3: The Language of Control
Examines Neuro-Linguistic Programming techniques in political speech, the CIA’s 1967 weaponization of the phrase “conspiracy theory,” the UK Nudge Unit’s deployment of fear messaging during COVID-19, and Cambridge Analytica’s industrial-scale psychographic profiling.
Chapter 4: Manufactured Crisis
From the Paris grain shortage of 1847 to the Gulf of Tonkin fabrication, the 2008 housing crisis, and the supply chain collapse of 2020-2021. Documents how crises are used to transfer wealth and justify policy that could not otherwise be enacted.
Chapter 5: The Controlled Opposition
COINTELPRO, the astroturfing industry, the tobacco industry’s front organizations, and the phenomenon of the monetized dissident. Includes the structural analysis of how revolutionary movements receive handlers.
Chapter 6: The War Machine
Operation Northwoods, the revolving door between the Pentagon and defense contractors, the $880 billion defense budget, and the structural profitability of conflict.
Chapter 7: The Assassination of Inconvenient Men
The Church Committee’s assassination program findings, the pattern of financial reformers and their fates (Lincoln, Kennedy, Gaddafi, Hussein), and lawfare as the modern substitute for physical elimination.
Chapter 8: The Digital Hidden Hand
Surveillance capitalism, the NSA’s PRISM and XKeyscore programs, GCHQ’s Tempora program, China’s Social Credit System, the RESTRICT Act, and the architecture of behavioral control.
Chapter 9: The Prophecies That Came True
Seven claims once dismissed as conspiracy theories, now confirmed by declassified documents. A structural test for distinguishing genuine analysis from paranoid fantasy.
Chapter 10: Breaking the Spell
A practical guide to structural thinking, media literacy, financial literacy, and civic action. The most actionable chapter in the book.
Chapter 11: The Same Playbook, Different Flags
The UK (BBC, D-Notice, City of London, GCHQ Tempora, Iraq War dossier), the EU (democratic deficit, ECB and Greek crisis, Brussels lobbying), and Australia (Pine Gap, Whitlam dismissal, Murdoch concentration). Establishes that the patterns are structural, not American.
The Hidden Hand: Then and Now Back Book Cover
5. The Financial Architecture Appendix
Appendix A is one of the most substantive treatments of financial architecture in any book of this kind. It examines five trajectories for the future of money:
- CBDC and Programmable Money: The risks of programmability, the Canadian truckers precedent, and the structural implications of a fully surveilled payment system
- Decentralized Finance and Stablecoins: The structural promise and the structural reality
- Privacy-Preserving Digital Cash: Zero-knowledge proofs and the disappearance of cash
- Regulated Tokenization and Asset-Backed Currency: BlackRock, JPMorgan’s Onyx platform, and the financialization of real-world assets
- The Quantum Financial System Vision: Evaluated honestly as a Tier 4 cultural phenomenon, not endorsed
The appendix concludes with a clear statement of what genuine financial reform requires: democratic accountability for central banks, sovereign money creation, antitrust enforcement in finance, revolving door restrictions, and public banking alternatives.
6. What the Book Gets Right
- The structural framing is rigorous and consistent throughout
- The Standards of Evidence Rubric is applied without exception
- The international chapter (Ch. 11) significantly strengthens the central argument by demonstrating that the patterns are not American phenomena
- The QFS appendix is handled with intellectual honesty: the grievances are taken seriously, the resolution is critiqued structurally
- Trump is used as a structural example only, not as partisan commentary
- The 1926 source text is engaged with directly rather than avoided, and its antisemitic framing is rejected clearly and repeatedly
- No em dashes. Clean, declarative prose throughout
7. What Has Been Strengthened in This Edition
- International scope: Chapter 11 adds the UK, EU, and Australia, establishing the universal pattern
- Expanded index: All significant names, documents, programs, and concepts are now indexed with sub-entries and cross-references
- Manifesto epilogue: The closing is tightened into a direct, declarative framework for structural reform
- Back cover copy: Positions the book precisely for its target reader: “For readers of documented history, not comforting myths”
8. How It Compares to Similar Works
| Book | Approach | Evidence Standard | Structural Framing |
|---|---|---|---|
| The Hidden Hand: Then and Now | Structural analysis | Four-tier rubric, primary documents | Yes, explicit |
| Manufacturing Consent (Chomsky) | Propaganda model | Academic | Yes, institutional |
| The Power Elite (Mills) | Sociological | Academic | Yes, class-based |
| Tragedy and Hope (Quigley) | Historical | Academic | Yes, financial networks |
| The Age of Surveillance Capitalism (Zuboff) | Technology critique | Peer-reviewed | Partial |
| Most conspiracy genre books | Narrative | Anonymous sources, speculation | No |
The Hidden Hand occupies a distinct position: it applies the rigor of the academic tradition to the accessibility of the popular nonfiction format, with an explicit evidence standard that most works in either category lack.
9. Frequently Asked Questions
Is this a conspiracy theory book?
No. It is a structural analysis based entirely on declassified documents, congressional testimony, peer-reviewed research, and investigative journalism. Every significant claim is labeled with an evidence tier.
Does the book blame any ethnic or religious group?
Explicitly not. One of the book’s hard constraints is that no ethnic, religious, or racial group is assigned collective responsibility for the behavior of concentrated power.
What is the Standards of Evidence Rubric?
A four-tier system applied to every significant claim in the book, ranging from primary declassified documents (Tier 1) to contested interpretive claims (Tier 4). It allows readers to verify claims directly.
Is the Quantum Financial System endorsed in this book?
No. It is evaluated as a Tier 4 cultural phenomenon and critiqued structurally. The book argues that genuine financial reform requires democratic politics, not technological salvation.
What practical tools does the book provide?
Chapter 10 provides frameworks for structural thinking, media literacy, financial literacy, and civic action. The Epilogue provides a four-level framework for structural reform at the individual, community, institutional, and systemic levels.
Who are the key sources?
Church Committee Final Report, Operation Northwoods (declassified 1997), CIA Dispatch 1035-960 (1967), Gulf of Tonkin NSA documents (declassified 2005), Financial Crisis Inquiry Commission Report (2011), Durham Report (2023), Chilcot Inquiry (2016), and works by Chomsky, Quigley, Zuboff, Sutton, Friedman, and Mills.